Stig Information Assurance
Mission Assurance Categories MAC The Department of Defense has three 3 defined mission assurance categories. The guidance documentation obtained through this site can be used as the.
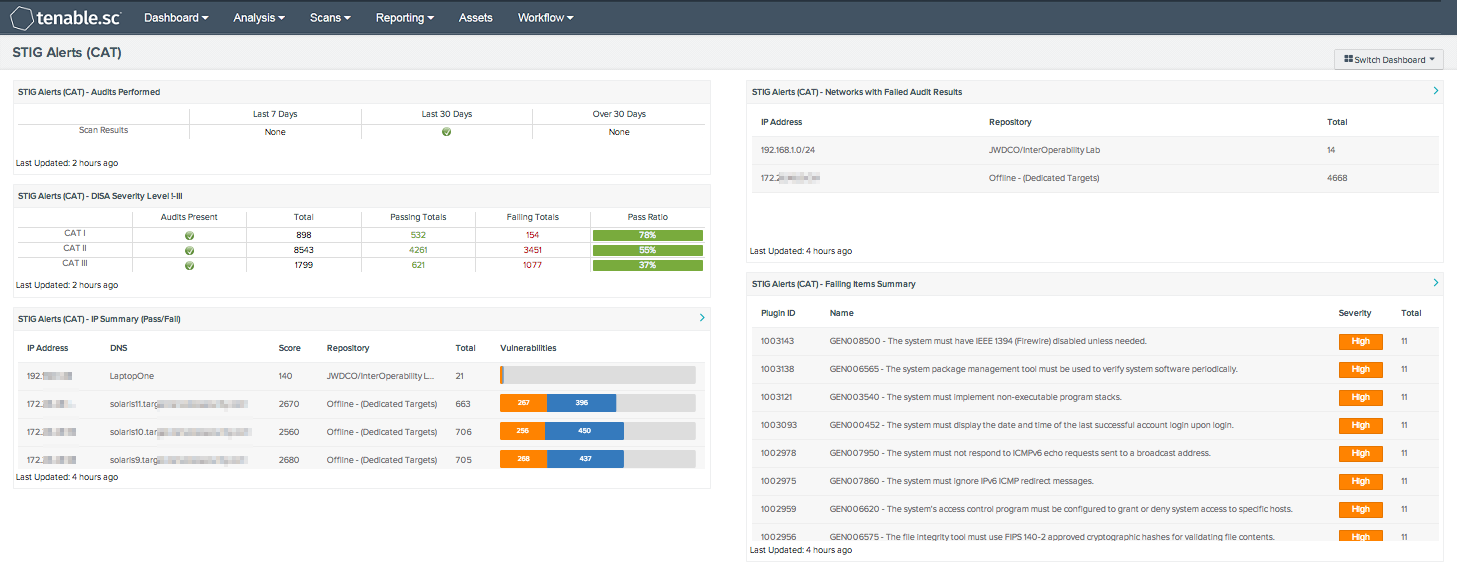
Stig Alerts By Cat Sc Dashboard Tenable
New releases of STIGs published prior to this change will include the legacy.

Stig information assurance. DISA STIGs Recognize CIS Benchmarks. Information Assurance A DISA CCRI Conceptual Framework 1. Guidance from the DoD Cloud Computing SRG indicates CIS Benchmarks are an acceptable alternative in place of STIGs - configuration standards for DoD Information Assurance IA and IA-enabled devicessystems.
NATO has endorsed the use of approved Best Practice to provide configuration guidance for information assurance products and services in use within NATO networks. During this one-day dynamic seminar students learn the best practices for designing implementing and deploying. For this STIG peripheral will mean any device that allows communication between a system and itself but is not directly operated by the system.
Information Assurance Overview STIG is an essential course for technical leads project managers testingQA personnel and other stakeholders who need to understand the issues and concepts associated with secure applications. A PROPOSED CONCEPTUAL FRAMEWORK FOR THE DISA CCRI PROCESS DISA CCRI Background Command Cyber Readiness Inspections CCRIs replaced Enhanced Compliance Validations ECVs in October 2009 as the mechanism by which Commanders would begin being held accountable for their respective network. Implementation guide geared to a specific product and version.
Azure provides automation and compliance dashboarding capabilities at cloud speed and scale allowing customers to reduce the heavy costs of compliance when they choose Azure. Disaletterkennyrembxstig-customer-support-mailboxmailmil Information Assurance Support Environment IASE disameaderembxiase-websitemailmil Enterprise Services Identity and Access Management IdAM DOD Visitor Please reference GSD contact Information Enterprise Directory Services EDS Please reference GSD contact Information. According to DISA STIGs are the configuration standards for DOD information assurance or IA and IA-enabled devicessystemsThe STIGs contain technical guidance to lock down information systemssoftware that might otherwise be vulnerable to a malicious computer attack.
New and updated STIGs are now being published with the modified content. However this document does not deal with devices found wholly contained within the main cabinet of the computer or with the exception of AB switches those devices connected via legacy parallel and serial interfaces. Contains all requirements that have been flagged as applicable for the product which have.
Test STIGs and test benchmarks were published from March through October 2020 to invite feedback. VoIP STIG V1R1 Field Security Operations 13 January 2004 Defense Information Systems Agency iii UNCLASSIFIED FORWARD AND ACKNOWLEDGEMENTS This Voice Over Internet Protocol VoIP Security Technical Implementation Guide STIG is published as a tool to assist in the improvement of the security of Department of Defense DOD. A STIG is a set of rules checklists and other best practices created by the Defense Information Systems Agency DISA to ensure compliance with Department of Defense DOD-mandated security requirements.
These configuration standards apply to DoD Information Assurance IA and IA-enabled devicessystems. As part of the proper Information Assurance IA controls the configuration settings are classified using Mission Assurance Category MAC Levels. The Center for Internet Security CIS builds CIS Benchmarks and CIS Hardened Images mapped to these guides to more easily assist with DISA STIG compliance.
STIG Report by MAC by Josef Weiss. 153 rows Excel. Systems handling information that is determined to be vital to the operational readiness or mission effectiveness of deployed and contingency forces in terms of both content and timeliness.
The DoD uses Security Technical Implementation Guide STIG audits to analyze risk and identify configuration vulnerabilities. Security technical implementation guide STIG Based on Department of Defense DoD policy and security controls. STIGs she continued are an operationally implementable compendium of DOD Information Assurance IA controls security regulations and best practices for securing IA or IA-enabled device operating systems networks applications and software.
STIGs are secure configuration standards for installation and maintenance of DoD Information Assurance IA and IA-enabled devices and systems. 1 Mission Assurance Category I MAC I. The currently available STIG based compliance standards are.
Security Operating Procedures SOPs for all systems supporting infrastructure and physical facilities must be written. These resources are provided to enable the user to comply with rules regulations best practices and federal laws. This page provides links to several national endorsed information assurance configuration guidance sites.
Fix Text F-34809r3_fix 1. The procedures must be readily available to both the Information Assurance Staff IAM IAO SA and all system users requiring information in the procedures to perform their jobs. DoD Instruction 851001 DoD Information Assurance Certification and Accreditation Process DIACAP.
These endpoints must be STIG compliant using the OS STIG and other applicable STIGs and must follow DoD requirements for remaining compliant. DISA is mandated to support and sustain the DoD Cyber Exchange formerly the Information Assurance Support Environment IASE as directed by DoDI 850001 and DODD 814001.
Information Assurance A Disa Ccri Conceptual Framework
Did You Read Your Stig Today Signal Magazine

Stig Compliance With Cis Aws Cloud Security Resources
Application Security And Development Security

Information Assurance A Disa Ccri Conceptual Framework

Security Technical Implementation Guide Stig The Signal Chief

Deploy Secure Cloud Native With Fips 140 2 Disa Stig Mirantis
Understanding Disa Stig Compliance Requirements Solarwinds

Stigs Scap And Data Metrics Pdf Free Download

Nutanix Stig S For Automated Security And Compliance Long White Virtual Clouds

How Stigs Impact Your Overall Security Program Segue Technologies
Security Technical Implementation Guide Stig The Signal Chief

What Is A Stig Security Technical Implementation Guide Youtube

Interview Stig Compliance Series Update
Stig Update Group Policy Objects Gpos For Security Technical Implementation Guides Stigs Convocourses

Code Dx Version 2 3 Tracks Disa Stig Compliance Code Dx
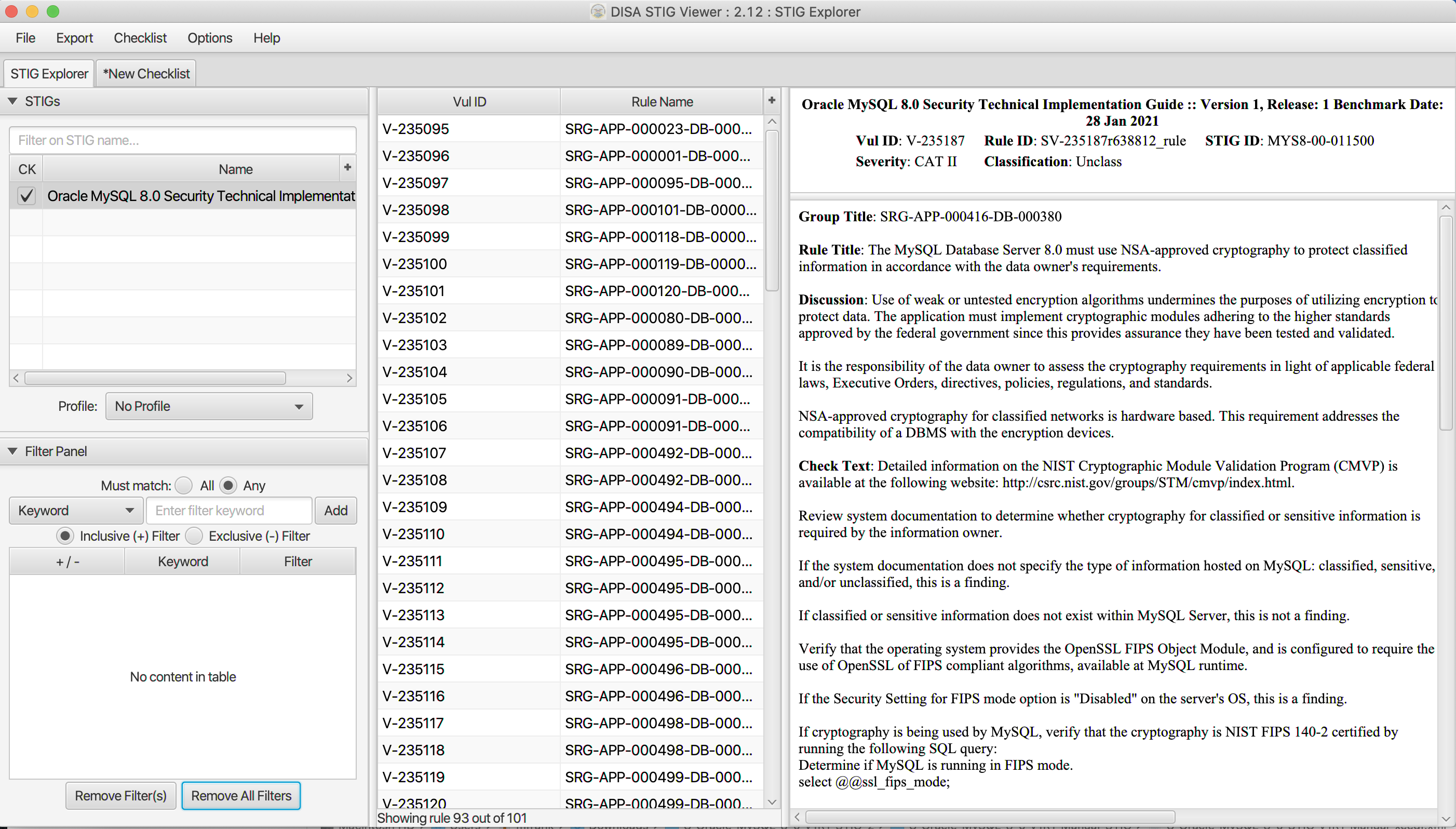
Mysql Mysql Security Technical Implementation Guide Stig
Automated Stig Hardening Finally Comes To Government It Security Info Watch


Posting Komentar untuk "Stig Information Assurance"