Information Security Management Audit Assurance Program
Perhaps the best rationale for a cyber assurance program is enablement of. Controls providing assurance that access to data software equipment and facilities is.
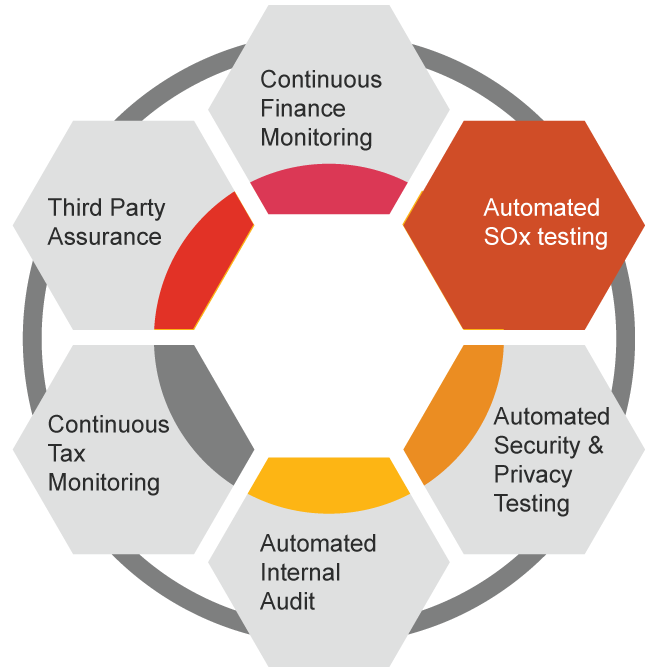
Continuous Monitoring Platform Audit Assurance Services Pwc
View Info-Sec-Mgmt-Audit-Program-22July10-Research-1doc from AUDITING 123 at University of Agriculture.
Information security management audit assurance program. Audit tests could include reviewing program plans and budgets interviewing key executives looking at security training material reviewing management test plans to evaluate the operating effectiveness of security efforts and their results reviewing managements communications to employees regarding the importance of security to the organization and how it contributes to long-term success. Regardless of information type Information Security can include paper-based and electronic formats and determines how information is processed stored transferred archived and destroyed. Behoud de controle over snelle en efficiënte toegang tot informatie met Managed IAM.
For Information Risk Management certification and training please visit us. Logical Security Audit Date_____ Operating Systems - Generic Assigned Sec. Are You A Hiring Manager Job Seeker or Desirous To Transit To Information Security and Assurance Career Path Here is All You Need To Know About The Job Requirements Skills SetExperience Reporting Line and Certifications Required For Information Security Cyber Security JobsRoles.
Job Requirements For Information Security Roles. The objective of the audit was to provide assurance to senior management on the effectiveness of governance over information technology IT security at Citizenship Immigration CIC including IT security risk management and specifically CICs Certification and Accreditation CA process. 2010 Personally identifiable information PII auditassurance program by.
Program based on an assurance cycle. Initials E ACCESS CONTROLS E 10 Account Management Objective. Ad Houd uw organisatie veilig met oplossingen van KPN Security uw partner in cybersecurity.
For 50 years and counting ISACA has been helping information systems governance control risk security auditassurance and business and cybersecurity professionals and enterprises succeed. Information Security Manager Job Description Version 11 Page 3 of 7 Classification. Our community of professionals is committed to lifetime learning career progression and sharing expertise for the benefit of individuals and organizations around the globe.
InfoSec Compliance Governance and Privacy Professionals. Moreover after an assurance program has been established internal audit andor compliance can also provide consultative support to management around cybersecurity. Security audits provide a fair and.
Controls providing assurance that security management is effective. Mobile computing security auditassurance program by. Our community of professionals is committed to lifetime learning career progression and sharing expertise for the benefit of individuals and organizations around the globe.
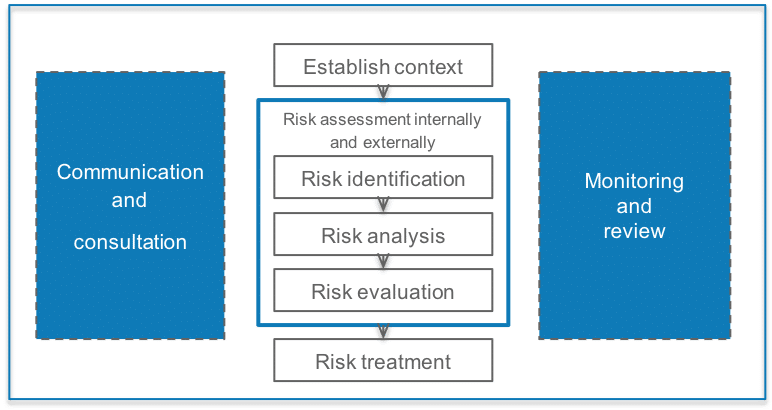
Information security risk management are set of policies procedural controls that organizations implement to secure informational assets safeguard them from cyberattacks. Information Security Management AuditAssurance. For 50 years and counting ISACA has been helping information systems governance control risk security auditassurance and business and cybersecurity professionals and enterprises succeed.
For 50 years and counting ISACA has been helping information systems governance control risk security auditassurance and business and cybersecurity professionals and enterprises succeed. The program is free to ISACA members and available for purchase to non-members for US 45. To ensure that appropriate controls are in place over the system level account management process.
Access to electronic resources restricted to Simmons University students faculty and staff. 2012 Crisis management auditassurance program by. Whether carried out internally or by independent external auditors IT audits should provide objective assurance of corporate IT governance risk management andor compliance.
IT information technology audits examine and evaluate organisations IT controls the policies and procedures that ensure information systems operate as intended. Examples include a security management program periodic risk assessments and validation and security control policies and procedures. Our community of professionals is committed to lifetime learning career progression and sharing expertise for the benefit of individuals and organizations around the globe.
It is among 14 auditassurance programs offered by ISACA aligned with COBIT 5 the leading framework for the governance and management of enterprise IT. It is part of the on-going process of defining and maintaining effective security policies. Information security management auditassurance program author Norm Kelson.
An Information security audit is a systematic measurable technical assessment of how the organizations security policy is employed. Audit Step Date Ref. Provide regular reporting on the current status of the information security program to enterprise risk teams senior business leaders and the board of directors as part of a strategic enterprise risk management program.
Page 6 PREPARED BY. For 50 years and counting ISACA has been helping information systems governance control risk security auditassurance and business and cybersecurity professionals and enterprises succeed. Our community of professionals is committed to lifetime learning career progression and sharing expertise for the benefit of individuals and organizations around the globe.
ISACA audit programs have been developed and reviewed by auditassurance professionals worldwide. Information and Cyber Security management is a critical component of any industry or sector and speaks to protecting the confidentiality integrity and availability of information assets.
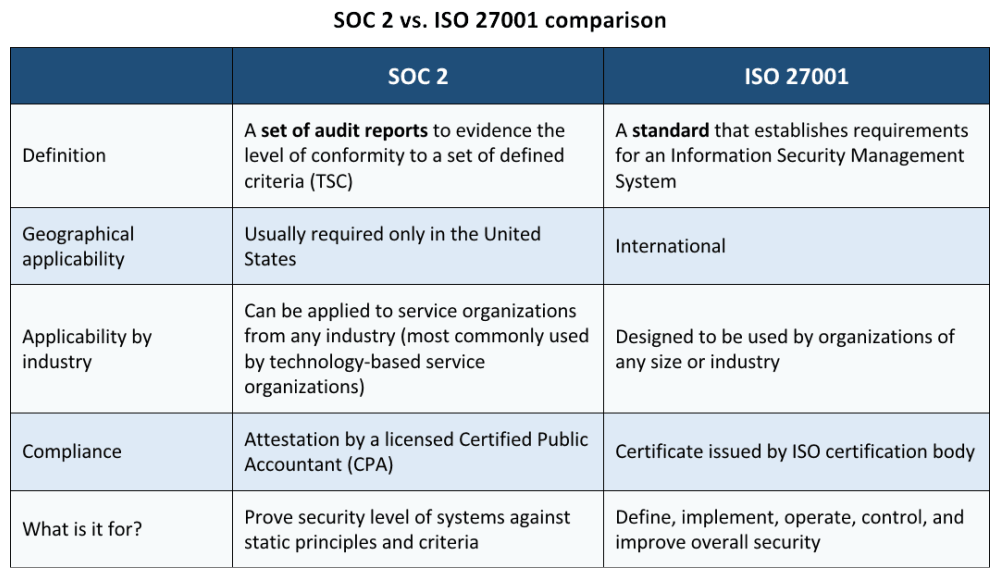
Soc 2 Vs Iso 27001 What Are The Differences
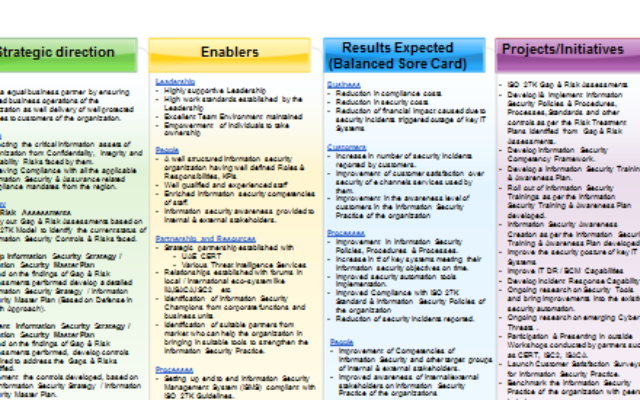
Assembling Your Information Security Master Plan The Digital Transformation People

Iso 27001 Assessments And Implementation Ntrust Advisory

Information Security Management At Hdfc Bank
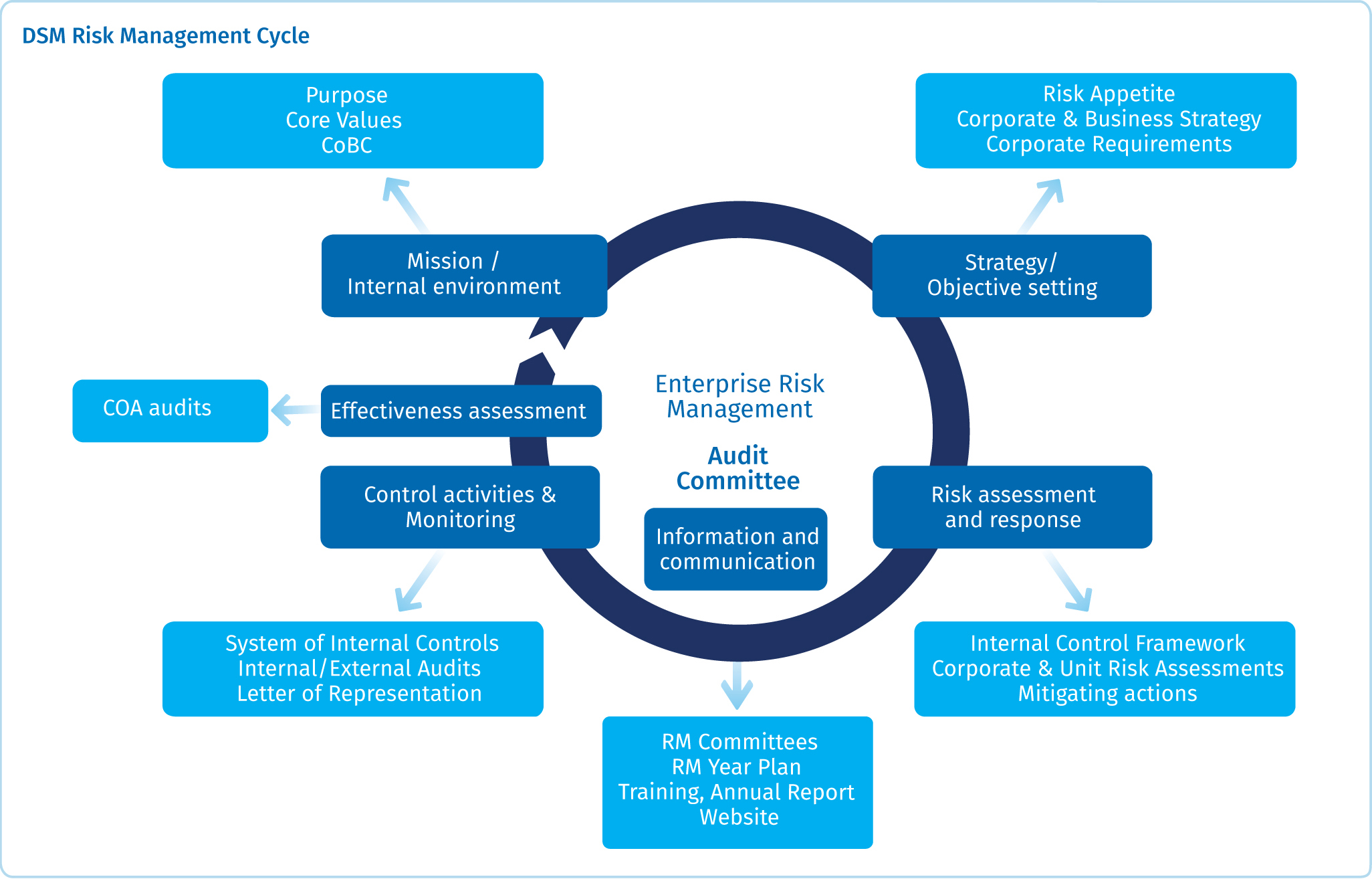
Risk Management Dsm Annual Report
Iso 27001 Annex A 14 System Acquisition Development And Maintenance
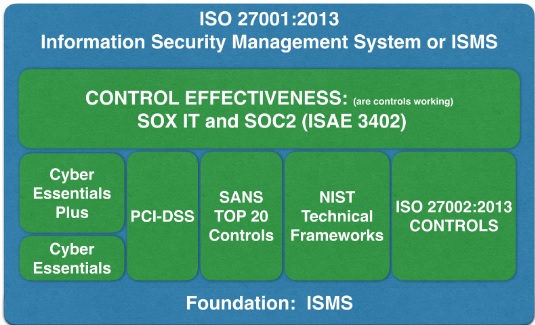
Iso 27001 Certification Vs Isae 3402 Soc 2 Assurance Report
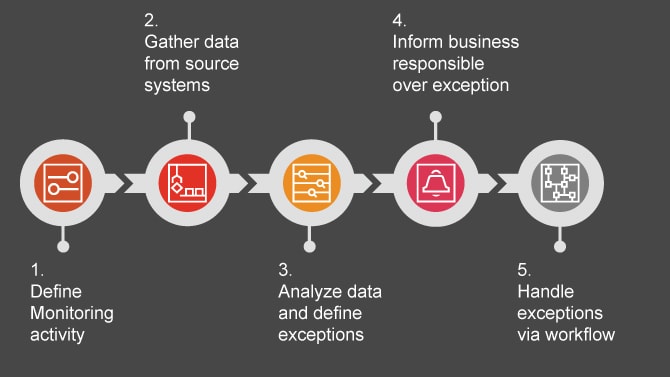
Continuous Monitoring Platform Audit Assurance Services Pwc
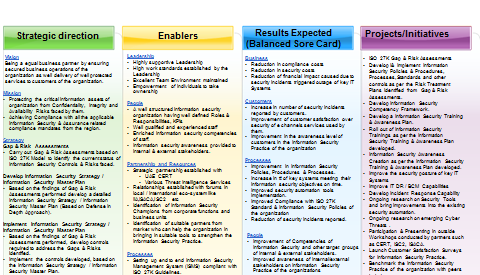
Assembling Your Information Security Master Plan The Digital Transformation People
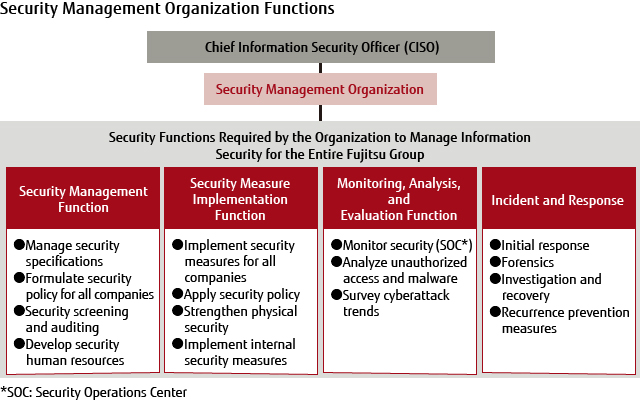
Information Security Fujitsu Global
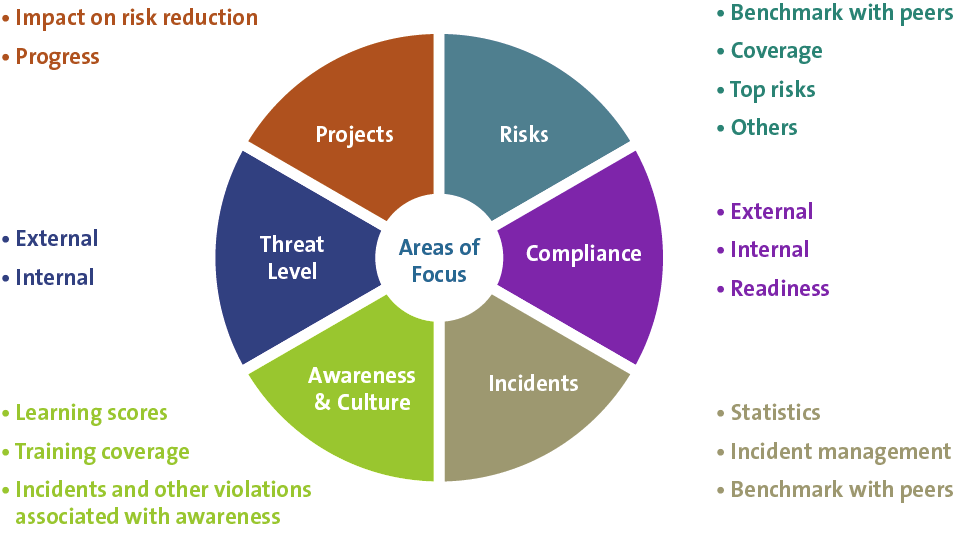
Cyber In The Boardroom Compact

Cyber Security Assurance And Audit Services Pwc In The Middle East
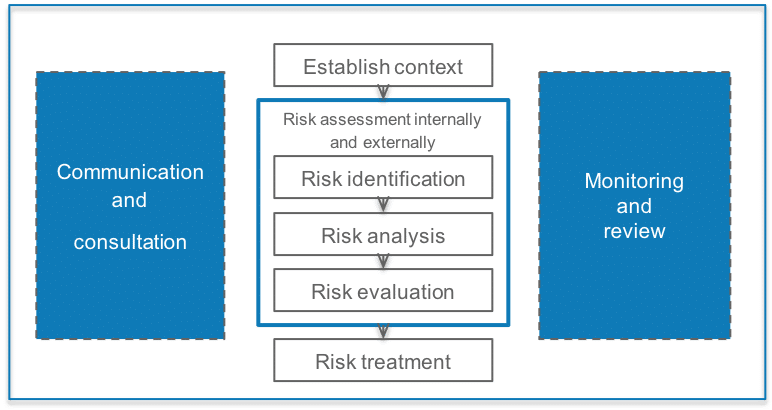
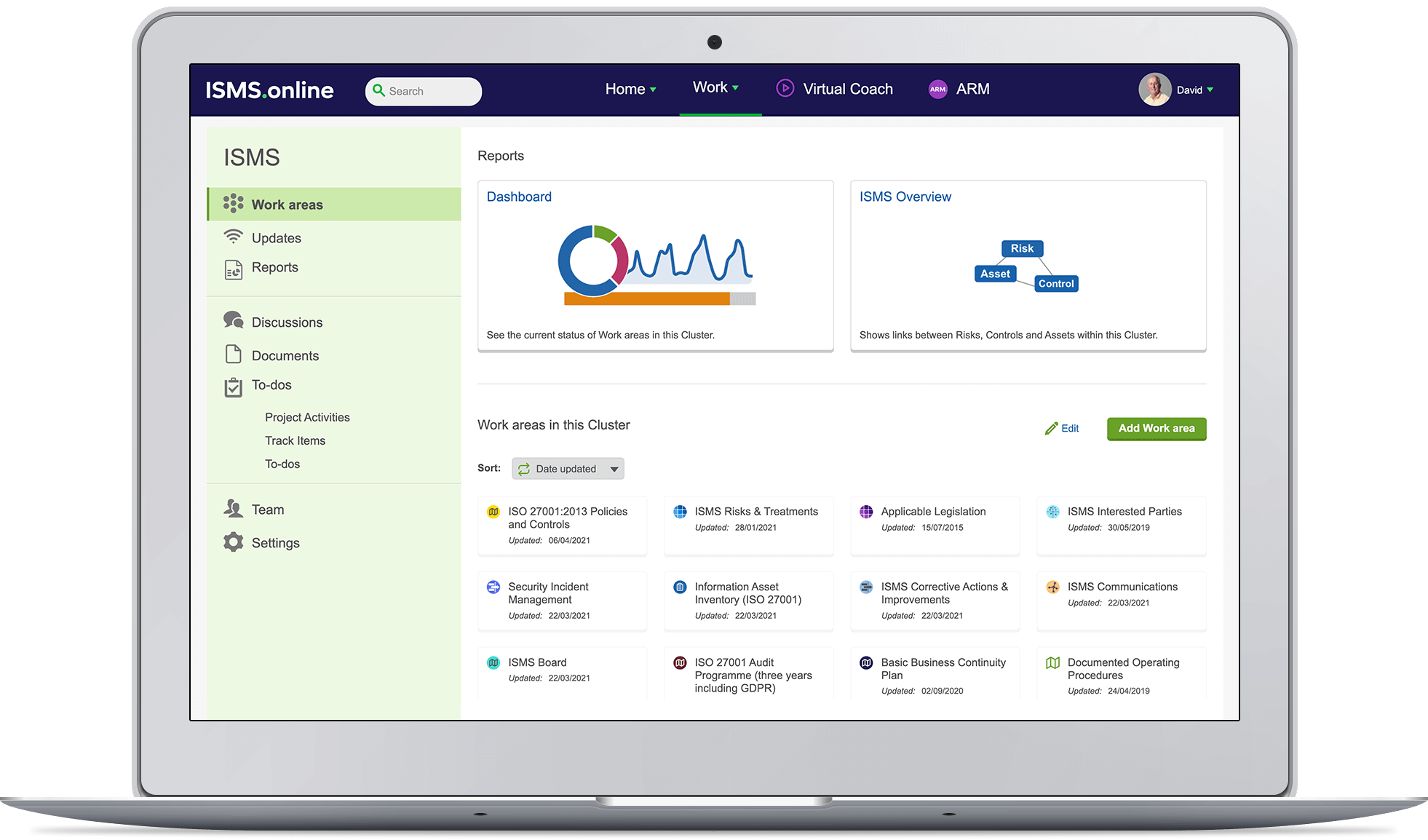
Information Security Risk Management Isms Online
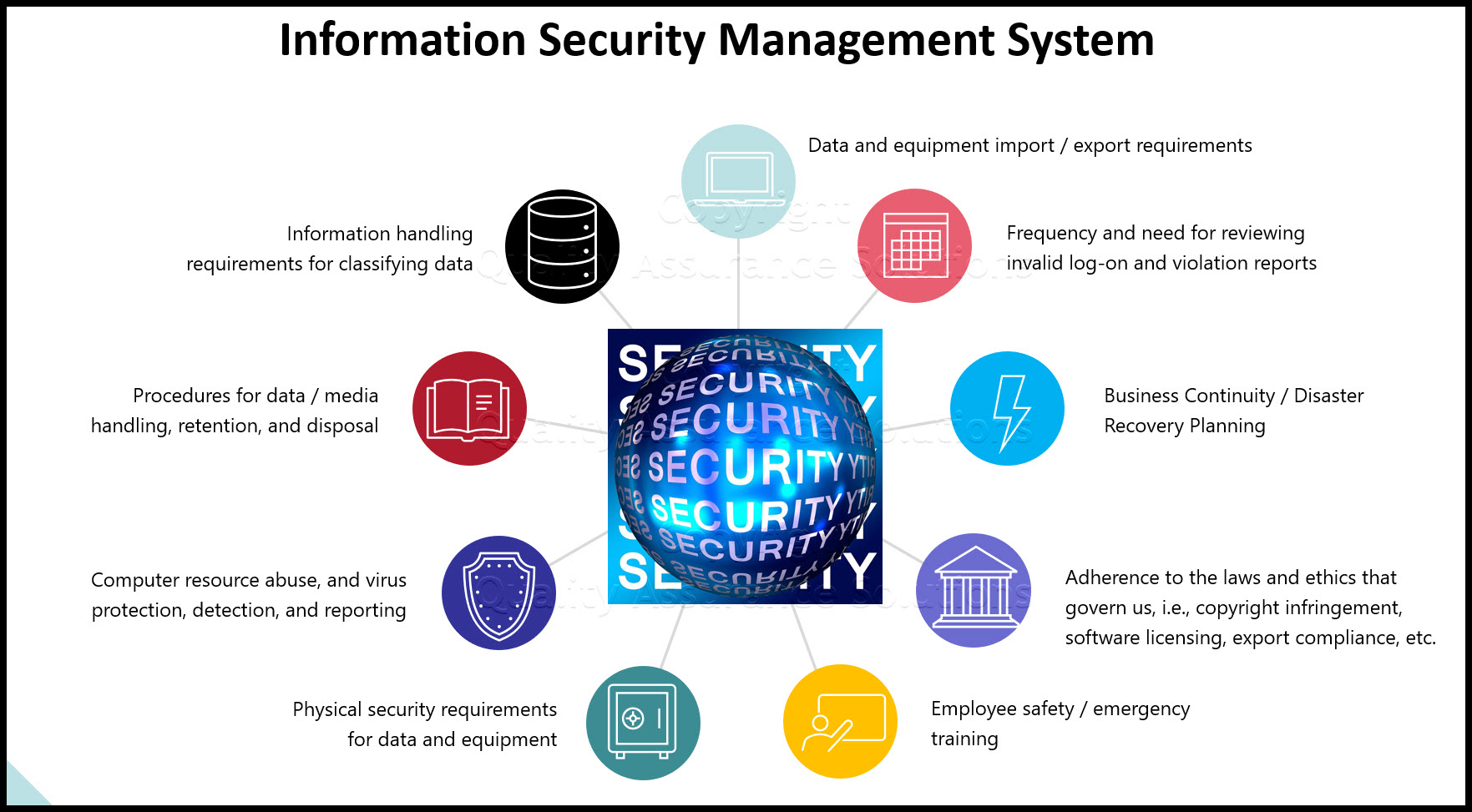
Information Security Management System
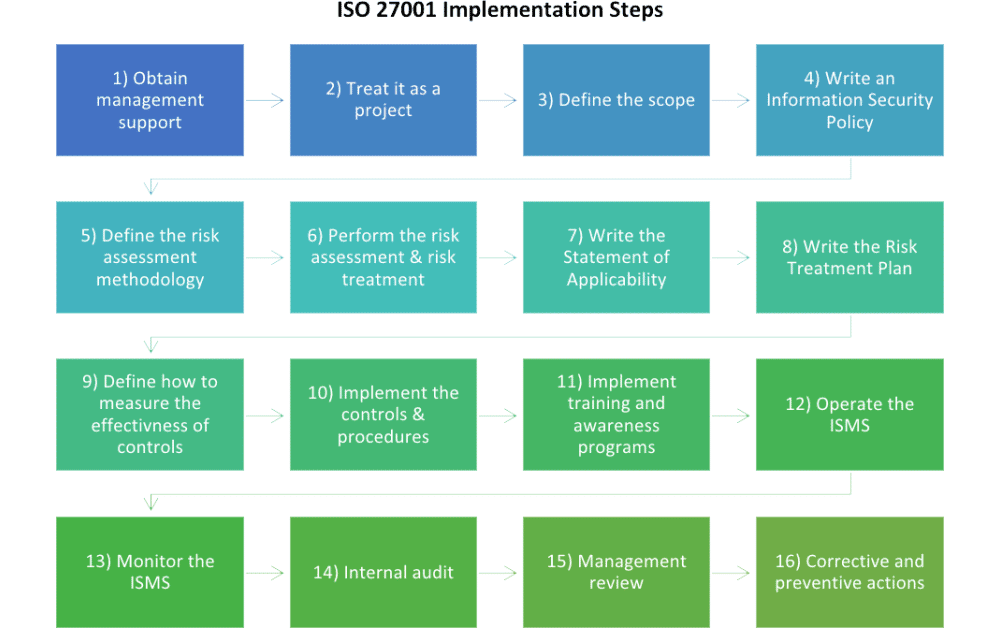
Iso 27001 Checklist 16 Steps For The Implementation

Developing The It Audit Plan Using Cobit 2019
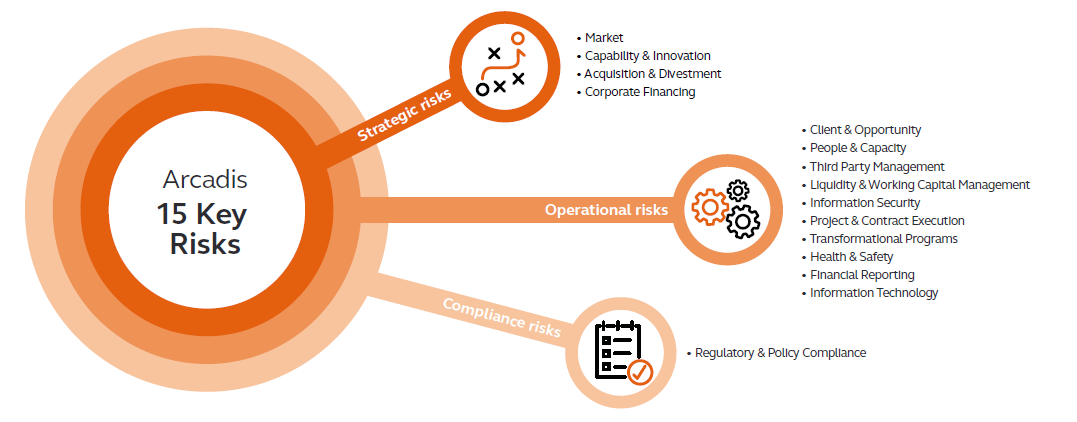
Enterprise Risk Management At Arcadis Arcadis

Developing The It Audit Plan Using Cobit 2019
Posting Komentar untuk "Information Security Management Audit Assurance Program"